First, I'm sorta reposting this from Left in Alabama:
The US v. The State of Alabama, George Bentley, Governor
I won't actually repost, just summarize complaint by the DOJ to be a nuclear warhead, ironclad maneuvering of the Supremacy Clause.
I have threatened to seek input building a model of the domestic intelligence apparatus.
So here I go -
The Domestic Intelligence and Security Apparatus under the Department of Homeland Security
Much of the following is also in this pdf http://opasylum.net/... , for those who might like a more inflected format (and hypertext links, I have not redone them here *yet)
Systemic Impunity under the Department of Homeland Security
How Networking Data in the Domestic Intelligence Apparatus Undermines 4th Amendment Protections
The following is a preface in the form of a free-form annotated bibliography. Those familiar with intelligence agencies will find more use in browsing these immediately and doing independent research.`
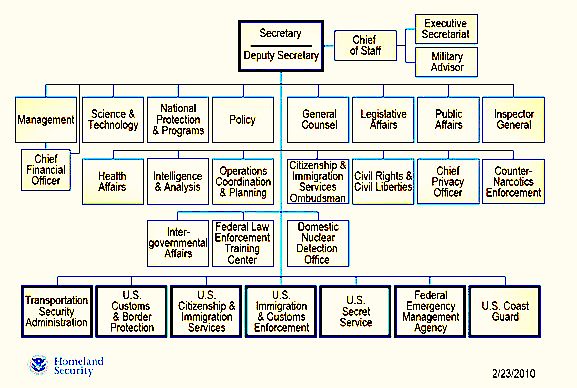
• Department of Homeland Security website infographic illustrating agency structure and hierarchy http://www.dhs.gov/...
The DHS is a federal agency of organizational administration for 7 primary constituent agencies (including a branch of the US Armed Forces)
Delegation of Immigration Authority Section 287(g) Immigration and Nationality Act (and referenced Template Memorandum of Agreement)
http://www.ice.gov/...
As phrased on the Department website:
U.S. Immigration and Customs Enforcement (ICE), the largest investigative agency in the Department of Homeland Security, enforces federal immigration laws as part of its homeland security mission. ICE works closely with federal, state and local law enforcement partners in this mission.
The 287(g) program, one of ICE’s top partnership initiatives, allows a state and local law enforcement entity to enter into a partnership with ICE, under a joint Memorandum of Agreement (MOA). The state or local entity receives delegated authority for immigration enforcement within their jurisdictions.
287(g) provides for DHS discretion in delegating authority, which the US Constitution reserves as the exclusive domain of the federal government, to local enforcement agencies in the form of service contracts. An outline of the character of these contracts can be found in the DHS site-provided “Template Memorandum of Agreement http://www.ice.gov/...)
Network Accountability for the Domestic Intelligence Apparatus Danielle Keats Citron and Frank Pasquale (http://www.hastingslawjournal.org/...)
From the Introduction:
A new domestic intelligence network has made vast amounts of data available to federal and state agencies and law enforcement officials. The network is anchored by “fusion centers,” novel sites of intergovernmental collaboration that generate and share intelligence and information. Several fusion centers have generated controversy for engaging in extraordinary measures that place citizens on watch lists, invade citizens’ privacy, and chill free expression. In addition to eroding civil liberties, fusion center overreach has resulted in wasted resources without concomitant gains in security.
While many scholars have assumed that this network represents a trade-off between security and civil liberties, our study of fusion centers suggests these goals are, in fact, mutually reinforcing. Too often, fusion centers’ structure has been based on clever legal strategies for avoiding extant strictures on information sharing, rather than on objective analysis of terror threats. The “information sharing environment” created by fusion centers has short-circuited traditional modes of agency accountability. Our twentieth century model of agency accountability cannot meaningfully address twenty-first-century agency coordination. [emphasis added]
They go on to submit that a system of checks on the networks themselves is the solution to the breakdown in pairing mobility with oversight.
A new concept of accountability—“network accountability”—is needed to address the shortcomings of fusion centers. Network accountability has technical, legal, and institutional dimensions. Technical standards can render data exchange between agencies in the network better subject to review. Legal redress mechanisms can speed the correction of inaccurate or inappropriate information. A robust strategy is necessary to institutionalize these aspects of network accountability.
This text also gives examples from domestic operations of misuse/diversion of resources toward undue surveillance of lawful non-violent activists, including a case involving the blacklisting (by way of terrorist “watch” list) of Catholic nuns.
Over a nineteen-month period in 2004 and 2005, Maryland state police conducted surveillance of human rights groups, peace activists, and death penalty opponents. As a result, fifty three nonviolent political activists were classified as “terrorists,” including two Catholic nuns and a Democratic candidate for local office.
A Maryland fusion center shared the erroneous terrorist classifications with federal drug enforcement and terrorist databases, as well as with the National Security Administration (NSA).
Bruce Fein, an associate deputy attorney general under Ronald Reagan quoted in the text, argued that fusion centers conceive the business of gathering and sharing intelligence as “synonymous with monitoring and disparaging political dissent and association protected by the First Amendment.” He noted “You can make an easy kind of a link that, if you have a protest group protesting a war where the cause that’s being fought against is international terrorism, you might have terrorism at that protest. You can almost argue that a protest against [the war] is a terrorist act.”
Immigration and Customs Enforcement (ICE) Secure Communities (SC) Standard Operating Procedures (SOP)
“Distributed for adoption by participating county and local law enforcement agencies” (http://epic.org/...)
The premise behind SC technology is biometric interoperability between the Department of Justice (DOJ) Federal Bureau of Investigation’s (FBI) Criminal Justice Information Services Division (CJIS) Integrated Automated Fingerprint Identification System (IAFIS) and the Department of Homeland Security’s (DHS) United States Visitor and Immigrant Status Indicator Technology’s (US-VISIT) Automated Biometric Identification System (IDENT). The IDENT/IAFIS Interoperability interface connects the FBI fingerprint system housed in the FBI’s CJIS Division with a DHS fingerprint system maintained by the US-VISIT program. Through IDENT/IAFIS Interoperability, a single query by a participating local law enforcement agency (LEA) checks both systems and confirms the identity and immigration status of a subject being processed during incarceration booking [emphasis original]
(SC is separate from the ICE 287(g) program and, as such, participation in SC will not adversely affect local agency participation in ICE 287(g) activities.)
[disclaimer]
Use of IDENT/IAFIS for the purposes of racial and/or ethnic profiling or other activity in violation of the Fourth Amendment of the United States Constitution is not permitted and may result in the suspension of the local jurisdiction engaged in the improper activity. ICE reserves the right to take appropriate remedial action if necessary.
The disclaimer fulfills the legal obligation of the DHS to disavow any codified practice of nationally unlawful targeting of individuals based on their apparent ethnicity. However the practice of the law, under local legislation such as AL HB 56, does not reflect ardor regarding prohibition of race-targeted apprehensions (or reports thereof). The DHS add particularly ICE are remiss in failing to address state policies which concern their jurisdiction; in the case of HB 56, it seems to have fallen to the Department of Justice (under pressure from minority. Immigrant’s rights, and other civil liberty monitors/interest groups to check Alabama’s overstepping of Constitutionally enumerated bounds.
o In this action, the United States seeks to declare invalid and preliminarily and permanently enjoin the enforcement of various provisions of House Bill 56, as amended and enacted by the State of Alabama, because those provisions are preempted by federal law and therefore violate the Supremacy Clause of the United States Constitution
o [HB56 and other measures establish State/County interaction (where the 287g contracts are instituted)
The Secure Communities Process
The SC process leverages existing FBI CJIS Division [Criminal Justice Information Services -which is “Nestled in the hills of West Virginia…a high-tech hub that supports crime-fighting and national security” according to the FBI website ] business practices to identify aliens convicted of a serious criminal offense. At the time of each booking, participating LEAs [law enforcement agencies] submit fingerprints to their SIB. The SIB electronically transmits the fingerprints to the FBI CJIS Division. However, National Fingerprint File (NFF) states send fingerprints to the FBI CJIS Division only at the time of the subject’s initial arrest. Thereafter, criminal bookings occurring subsequent to an initial arrest in NFF states result in transmission of a Criminal Print IDENT (CPI) file maintenance message to the FBI CJIS Division
Integrated Automated Fingerprint Identification System (IAFIS) and the Automated Biometric Identification System (IDENT) Interoperability Report . http://www.dhs.gov/...
This FOUO directive-type memorandum underlines the Federal legislation which backs the formation of IDENT/IAFIS. From the document text:
o U SA PATRIOT Act of 2001 : Requires the ability to check the criminal history records for alien visa applicants, alien admissibility, and alien deportability.
o Homeland Security Act of 2002: Requires DI-3 S to oversee and coordinate DHS programs for and relationships with state and local governments.
o Enhanced Border Securitv and Visa Reform Act of 2002: Requires an interoperable law enforcement and intelligence data system, and the ability to update IDENT as a critical watch list with known and suspected terrorist information.
o Intelligence Reform and Terrorism Prevention Act of 2004: Requires creation of an information sharing environment to share terrorism information across the homeland security, law enforcement, and intelligence communities at all levels of government and the private sector, and accelerated development of an integrated electronic biometric entry-exit screening system (i.e., the Entry / Exit system).
o Given the new, post-September 11 environment in which the federal government is operating, additional requirements and security concerns can and must be identified.
o ICE ACCESS ( Agreements of Cooperation in Communities to Enhance Safety and Security) Program (http://www.ice.gov/...)
o See Immigration and Naturalization Act section 287(g) on the delegation of authority by federal agencies to local law enforcement as the legal provision for ACCESS (and others)


