Or, How Greenwald and Snowden Sold the Public on Pre-Conspiracy Theory
INTRODUCTION
It seems that over the last year of reporting from numerous media outlets we've heard a lot of what seems like scary stuff but we have not heard of a single, intentional Constitutional violation. Snowden and his reporters have had over a year and access to tens of thousands, if not hundreds of thousands, of Top Secret national security files to prove just one intentional violation of the Constitution. They haven't. If anything, Snowden and Greenwald and Poitras and Gellman and Applebaum and all of the others have established that there is an exceedingly functional and exceptional oversight mechanism in place that is three branches wide, thousands of regulations and laws deep and millions of miles of red tape tall.
On top of the three branches of Government providing oversight, we have whistleblowing procedures, including Inspectors General and the Office of Special Counsel, as well as the media, a Civil Liberties Protection Officer and the Obama Administration's new Privacy and Civil Liberties Oversight Board. That's a seven-layered bean dip of privacy protection that we wouldn't know about without Snowden. Yet, even without proof of one tiny intentional Constitutional violation, Snowden and Greenwald have managed to stir up quite a bit of public controversy. How?
I believe there are a number of reasons for this and want to touch on a few of them before tackling the reason that gave birth to the main title of this diary. Let's start with the media.
A Compliant Media. How else do you explain the fact that after a year of Greenwald's loudly calling the NSA metadata program some form or other of Big Brother, it only now surfaces that Greenwald (1) Thoroughly vetted the program when it was first leaked in 2006, (2) Offered a few reasons why the 2006-version of the metadata program was unconstitutional or illegal, (3) Saw all of his suggestions implemented between 2006 and 2013, and (4) nobody in the media has called Greenwald out for his amazing goal-post shifting? How has the media let a year slip by without calling out Greenwald about the Smith v. Maryland case, which held the Government's collection of metadata from even known, identified persons to be Constitutional ... back in 1979?
I have personally searched every Greenwald-authored or co-authored article in The Guardian from June 2013 to June 2014 and every Greenwald-authored or co-authored article in TheIntercept from its inception, and the Smith v. Maryland case is not mentioned once. Not once! It is the Roe v. Wade of metadata cases, and the media has let Greenwald avoid the topic for going on 13 months.
Why has nobody in the media asked Greenwald why he keeps claiming that NSA Director James Clapper deceived Congress with his March 2013 testimony? Greenwald knows very well that Congress was briefed on the program in 2009, 2010 and 2011. He knows that a majority of Congress voted to re-authorize the program on multiple occasions. Greenwald repeats this same myth in chapter one of his book. Yet, the media has not questioned him about it.
I believe that one of the reasons the media has been so compliant is that this is the specialized milleu of the "national security reporter." National security reporters want their own lottery ticket. Greenwald has turned Snowden into a money making machine with media opportunities, a book, public appearances, awards, and a new quarter-of-a-billion-dollar website. Why would a journalist criticize Greenwald and possibly turn off the next Snowden? It has been a win-win situtation for Greenwald (not quite the same for Snowden).
There's also the "Reverse-Nixonian" meme that Tommy Christopher noticed while he was writing for Mediate. The meme basically looks like this: Journalists are always right (even when they're wrong), and Government is always wrong (even when it's right). This is especially true after the Obama Administration went after people like John Kiriakou (who outed a CIA agent) and subpoenaed Fox News because of material leaked by Stephen Jin-Woo Kim (who gave Fox News Top Secret information dealing with North Korea, which Fox News then reported). Reporters have banded together, in my opinion, much like the NRA, vociferously decrying any potential intervention on the Government's part into their business.
Difficult, Technical Material. How many of us know how computers work? I don't. They are magic thunderboxes to me. How many of us know how to perform even the most basic computer hack? Yet, almost all of us know how a gun works and how to rob a bank. Technology is the difference in reporting in the two areas. It isn't hard to interview a bank robber. On the other hand, dealing with an expert like Snowden can be tricky. Likewise, how many reporters have gone to law school and feel comfortable enough to challenge Glenn Greenwald's proclamations about the law? How many reporters know about the Smith v. Maryland case or could find and analyze it? At best, a reporter might feel adequate in one of those areas unless he or she obtained the services of experts to assist them in preparing questions and stories. That is an expense newspapers would rather not pay, so why not a story re-hashing Iraq or immigration?
The NSA Cannot Effectively Fight Back. If it is not a commonly known maxim, it should be: "Spy failures are secret, but spy success stories are TOP SECRET." You don't want your opponent to know how you have disabled their nuclear reactors (Iran) or shot down their best and most effective Admiral (Japan during WWII) or effectively targeted their terrorists (Afghanistan, Yemen, Pakistan). Even in court, the NSA cannot reveal all of its secrets. Government lawyers cannot bandy about the successes to a judge because that could possibly open the door to opposing lawyers finding out those Top Secrets. See, e.g., Rule of Optional Completeness; "Open Door" Doctrine. I'm not saying shed a tear for the powerless, bullied NSA; rather, just keep in mind the reasons the NSA cannot always fight back. When asked to comment on a breaking story, the NSA must necessarily take some time to weigh what they have to say, and, I would guess, a "no comment" or limited response is standard procedure, as they know Russian, Chinese and terrorist ears would be listening to the response and using any useful information.
As a collorary to this proposition, there's the "Clapper is a liar" meme. It is true that he did not truthfully answer the question posed to him by Senator Ron Wyden. On the other hand, it is false to say that he deceived Congress, and it is just as false to claim that he committed perjury. He did neither. On the other hand, he was under a duty as Director of National Security to not expose national secrets. What was he supposed to do when confronted with the spy version of the "Have you stopped beating your wife" question? It was a Catch-22, no-win situation for him.
It's Easy to Sell Gloom and Doom to Teenagers and Young Adults. It's like selling over-acting to The Disney Channel. Producer: "I'd like to pitch a show that is chock full of pre-teen over-acting." Disney Executive: "I'll take a dozen, no make that two dozen!" These kids were in diapers or Garanimals when the NSA metadata program was leaked and then thoroughly and publicly vetted in 2006. They don't know that it was a thing. So this is something fresh and exciting for them.
Moreover, every generation believes that the world is coming to an end, and that there's is the generation that must fight the most epic battle against evil. Read a newspaper from 1920 or a Charles Dickens novel from 1850. They all cover the same ground, different issues. [My personal favorites are any transcripts of the last three Republican National Conventions during the years FDR sought re-election. The Republicans are the most venal, venomous, nihilistic Cassandras I have ever heard. "This country will be dead and buried in a fortnight!"] The internet is also part and parcel of the last two generations' existence. They are less likely to get their news at 6:00 pm and read a lengthy and ponderous article on the subject in a newspaper the next morning when they can just go to their friend's Facebook page and see what he or she has liked.
Capability Versus Reality. Capabilities are scary. There's no doubt about that. Our Government arms as many as two million individuals with various weapons, including tanks, missiles and jet fighters, swears them to allegiance and could order them to attack Kenosha, Wisconsin. The Government has enough nuclear missile capability to make the planet uninhabitable for humans. The CDC has stockpiles of biological matter that could kill billions. Even the lowly Post Office, that most American of institutions, could be ordered to read all of the 158 billion pieces of mail that has gone through it. Have you been in the back of a Post Office? Those are secret rooms, kept secure, with you on the outside, and inside the Post Office has complete control of your mail. (By the way, the Post Office is keeping metadata for every piece of mail currently sent. But nobody seems to worry about that.) What keeps doomsday from happening? The Rule of Law. We live in a society of laws that keeps the capable from becoming the real. How this perception got so warped when it comes to NSA spying is an interesting subject. To have one of those nightmare scenarios described above occur, we'd need a future conspiracy to break American laws.
And that's what Snowden and Greenwald have been peddling. It isn't even Conspiracy Theory. There's no current conspiracy or past conspiracy involving these current programs with the changes made since 2006. It is pre-Conspiracy Theory. There has to be a future conspiracy between Government officials to violate the myriad laws and regulations and evade the oversight in order to violate the rights of Americans. How did we come to this?
Since 1979, the Government has been legally and constitutionally allowed to obtain the telephone metadata of even known, identified individuals. In the Smith v. Maryland, 442 U.S. 735, 744 (1979) case, the United States Supreme Court held that we don't have a reasonable expectation to privacy when it comes to the business records of others (telephone carriers) and to information that we have voluntarily handed over to third parties.
So, the one "capability" that Snowden exposed that deals with Americans and was actual "reality" has been legal and constitutional for thirty-five years.
In fact, the Supreme Court has passed on hearing a multitude of cases dealing with the Post Office obtaining metadata. In United States v. Choate, 576 F.2d 165 (9th Cir.), cert.denied, 99 S.Ct. 350 (1978), the Federal Circuit Court held that postal inspectors could copy and maintain records of the information on the outside of sealed envelopes. Other circuits have agreed with the ruling, which is probably why the Supreme Court has passed on the issue, denying certiorari every time. See United States v. Leonard, 524 F.2d 1076 (2d Cir. 1975), cert. denied, 425 U.S. 958 (1976); United States v. Balistrieri, 403 F.2d 472 (7th Cir. 1968), cert. denied, 402 U.S. 953 (1971). Basically, postal inspectors can keep track of the "metadata" of letters mailed in the United States; they just could not open the letters and view the contents.
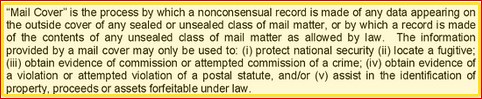
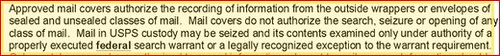
Postal "metadata" includes not just the "when" of the communication, but also, written on the envelope, the "who," including the author and addressee. That, it seems to me, is about 100x more invasive than the current, anonymous NSA telephone metadata program. The outside of envelopes normally include names and physical locations. The decision in Cohen was rendered forty-seven years ago. Like the Smith v. Maryland case, Cohen is still good law. Here is a pair of screengrabs from a New York Times story on Mail Covers:
Bob Cesca at the dailybanter.com has repeatedly shown how Greenwald and others have put the scary "capabilities" at the top of their articles and hid the "reality" down in paragraph twenty-three. In fact, this entire argument should be attributed to Cesca, as he has done the hands-on review of the NSA articles.
Scare Words and Phrases. The reason this diary exists is because of another diary on daily kos which attempted to create fear about something ominously called "Operation Minerva." The actual operation, itself, was quite innocuous, and, in fact, dealt with topics the Government should be interested in such as Climate Change (and represented the kind of research that only used to scare Republicans). Yet, people became afraid of this Government project because, I think, it had a very vague and somewhat unsettling name.
I have noticed this happen frequently with journalists reporting on the Snowden files. The average article of this type includes a headline or first paragraph containing the suspicious name of an operation or procedure, placed, I believe, intentionally, to generate fear and hatred of the Government (or at least encourage site traffic). You have to read much deeper into the article to find out that the "Armageddon Project"--or whatever silly name was given to it--actually involves spying in Yemen, Pakistan and Afghanistan or something along those lines. Additionally, there has been a cornucopia of hyperbolic scare words and phrases cribbed from Hollywood and fiction that have no relation to what's actually happened or is actually happening. Here is my short list of the best of the best scare words and phrases:
1984: George Orwell wrote this book of fiction, and some say it is coming true, even though the author's skill at prophecy can more or less be judged by the book's title. Still, in a "Price Is Right" kind of way, Orwell is on the money because he came closest to predicting the start of the surviellance state without going over. Another writer proclaimed that the world would end when a giant snake ate it. Still another author claimed that the US Government would become tyrannical and unjust, leading to wholesale carnage. Timothy McVeigh liked that story. Those are all in books. Also, there's this one about some joker who takes over Gotham City and blows up a hosptial. Now that I could see happening. Yeah, but really, there are lots of books.
BIG BROTHER: Term used to describe the United States Government by people who don't like or don't understand the United States Government. From the George Orwell book--see 1984 above--it is used by Snowden himself to describe how the Government is watching "everything" that you do and how the next generation will "never know a moment of privacy." Pure tinfoil hat drama.
BOUNDLESS INFORMANT: Scary name given to program that provides cute little pie chart-like pictures of where the NSA is obtaining intelligence. The Guardian, after scaring people with the name, reported this about the program: "The focus of the internal NSA tool is on counting and categorizing the records of communications, known as metadata, rather than the content of an email or instant message. (emphasis added). No intentional violation of the United States Constitution has been attributed to the Five Eyes program.
CAPABLE: (See COULD below) The ability to do something whether or not that something is actually happening now. (Related: "If the Government is capable of doing it, it is doing it." This argument fails to take into account such things as the fact that the Earth exists and is not a nuclear wasteland, as well as the very factual and very public existence of White Supremacist groups and Fox News.)
COULD: The state of things that might happen. As relevant to Snowden, "could" necessarily requires belief in a pre-Conspiracy Theory, in which future Government officials combine to violate the Constitution, Federal laws, agency rules and regulations and caselaw, all the while avoiding whistleblowers, the media, agency procedures to combat illegality (i.e., the new "buddy system"; keystroke audits), Congressional oversight and Executive Branch oversight. Believers in "COULD" do not believe in the Rule of Law.
FIVE EYES: The name given to an alliance between five strong allies to share and cooperate when it comes to national security intelligence. The name bespeaks a kind of scary spidery image with the five eyes. If it was an agricultural trade agreement, I guess it might be called "The Five Bellies," which would be less scary. No intentional violation of the United States Constitution has been attributed to the Five Eyes program. Don't we want countries to cooperate with us? Also, doesn't it increase the likelihood of whistleblowing if a real problem arises?
LAMESTREAM MEDIA: Also known as the "corporate media," "punditocracy," or the "beltway media," but only if a reporter in that particular organization questions Snowden or Greenwald the slightest bit. The aim, I guess, is to stigmatize all media, even though, like everything else, some are good and journalistic and some are bad and propagandistic.
MUSCULAR Is another scary sounding name for an NSA program, but, again, it has little bearing on the United States Constitution. Reports were that it was a world-wide program to tap into Google and Yahoo, but if you look at the Washington Post piece on the subject, you have to scroll down to the end of the page in a very long article to find out that it deals with "foreign data." Not as quite so far down the page, but pretty far nonetheless, the reporter notes that the data collection occurs "on British territory." No intentional violation of the United States Constitution has been attributed to the Five Eyes program.
NAZI: Ruling party in Germany immediately before and during the Second World War. The proximate cause of millions of deaths and a very poor and distasteful usage when describing the United States.
OPERATION MINERVA: A grant program from the Department of Defense to research certain key questions, including the effect of Climate Change on various populations. No violation of the United States Constitution has been attributed to Operation Minerva. The name may be scary, but the idea is a good one. Moreover, isn't it the Republicans who are against science and research?
PRISM: Giant hoopla, big nothingburger. No violation of the United States Constitution has been attributed to the PRISM program. And Barton Gellman of the Washington Post, to his credit, included this paragraph at the very top of his reporting: "The top-secret PRISM program allows the U.S. intelligence community to gain access from nine Internet companies to a wide range of digital information, including e-mails and stored data, on foreign targets operating outside the United States." (emphasis added).
RUBBER-STAMP: The mostly satirical but still scary name given to a judicial body that okays any request for authority from the Government. Snowden's stenographers frequently use this term when describing the FISA courts without describing the actual process. For, if they did describe the actual process, it would be readily apparent that the courts are anything but a rubber stamp. The process to obtain a court order takes a lot of time, and many requests are weeded out before the judges get a chance to rule on them. These are acutally very like "Advisory Opinions," with the court taking a hands-on approach to ensuring that privacy is protected. A FISA court judge estimated that up to 27% of the initial requests don't make it to final judicial approval, at least not without modifications. Additionally, the FISA court not only approves the start of any program, it also periodically evalutes them to ensure compliance.
STASI: Secret police in East Germany after the Second World War. Usage of this term to describe the United States should automatically require the user to be placed for re-education. Um, I mean, "to get a real education."
XKEYSCORE: A perfect example of the conflation of "capabilities" with "reality." No intentional violation of the United States Constitution has been attributed to the XKeyscore program. It is like the google search engine for spies, as the NSA agent can look for specific terms or people. In a masterstroke of deception, Glenn Greenwald reported on this program with the strange name in The Guardian with a fifty-paragraph article that didn't mention the following until the forty-sixth stanza:
In a statement to the Guardian, the NSA said: "NSA's activities are focused and specifically deployed against – and only against – legitimate foreign intelligence targets in response to requirements that our leaders need for information necessary to protect our nation and its interests.
"XKeyscore is used as a part of NSA's lawful foreign signals intelligence collection system.


