The FBI has a secret weapon in the War on Cybercrime: its own custom Trojan Horse. The bureau used the spyware to intercept an e-mail bomb threat in 2007 by a high school student in Washington state. Exploiting web browser vulnerabilities, it can be downloaded onto a suspect’s computer when an infected link is clicked on.
A sophisticated FBI-produced spyware program has played a crucial behind-the-scenes role in federal investigations into extortion plots, terrorist threats and hacker attacks in cases stretching back at least seven years, newly declassified documents show.
More after the flip:
As first reported by Wired.com, the software, called a "computer and internet protocol address verifier, or CIPAV", is designed to infiltrate a target's computer and gather a wide range of information, which it secretly sends to an FBI server in eastern Virginia. The FBI's use of the spyware surfaced in 2007 when the bureau used it to track e-mailed bomb threats against a Washington state high school to a 15-year-old student.
But the documents released Thursday under the Freedom of Information Act show the FBI has quietly obtained court authorization to deploy the CIPAV in a wide variety of cases, ranging from major hacker investigations, to someone posing as an FBI agent online. Shortly after its launch, the program became so popular with federal law enforcement that Justice Department lawyers in Washington warned that overuse of the novel technique could result in its electronic evidence being thrown out of court in some cases.
An application to approve CIPAV was sent by the FBI to the FISA court in 2005.
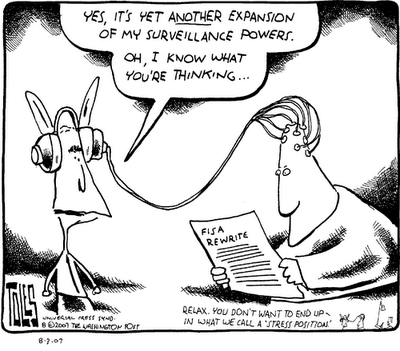
The FBI has reportedly sought the go-ahead to use a custom spyware package to bug terrorists and other national security suspects. Indirect evidence suggests that the request was likely to have been approved. An application to use the Computer and Internet Protocol Address Verifier (CIPAV) spyware program was sought from the secretive Foreign Intelligence Surveillance Court in 2005, according to papers obtained by Wired after filling a Freedom of Information Act request.
Among the reams of papers released in response to Wired's request (largely composed of internal emails and technical documents) are affidavits submitted by the FBI to the FISC star chamber to use the CIPAV package. The software is designed to log a target's internet use, recording every IP address a suspect computer communicates with. It also performs an inventory of operating systems, installed and running applications and logs open ports, IP addresses and Mac addresses of targeted PCs.
<...>
US authorities are far from alone in seeking approval for the use of "remote forensic software" (AKA a law enforcement Trojan) to bug the PCs of terrorist suspects. The German government is reportedly in the process of hiring coders to develop "white hat" malware capable of covertly hacking into PCs ahead of plans to change German law to allow the practice. Proposals by German firm Digitask to develop software to intercept Skype VoIP communications and SSL transmissions leaked onto the net last month.
The FBI's spyware adds an additional challenge to an internet where the size and frequency of network infections has escalated. For instance, a 1.9 million computer botnet was recently uncovered by the IT security company Finjan.
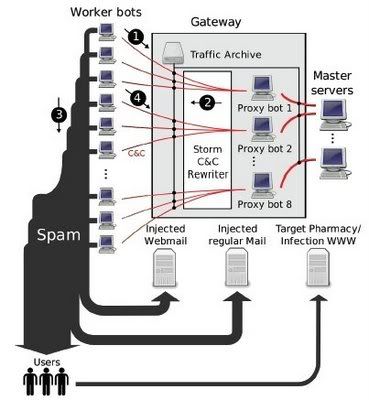
It is the largest network of hijacked computers – or botnet – to have been discovered. to date. It is at least four times larger than botnets that have been discovered in the past, which have tended to include 200,000 to 500,000 computers.
In the UK alone, more than 500 companies were caught in the network of infected machines, including both large and small businesses. Six UK local government computers were compromised, while in the US, computers at both federal and local government level were infiltrated, said Yuval Ben-Itzhak, chief executive of Finjan, the IT security company that discovered the network. He declined to name any of the businesses that were affected, but said they included some of the largest global corporations.
"With this many computers affected, everyone was there on the list – the US Federal government, big universities, very large public companies," Mr Ben-Itzhak said.
Finjan has provided the FBI and Metropolitan Police with information about the network but there has been no update on whether the law enforcement agencies have been able to track down the criminals. The server from which the botnet was run is no longer in operation, but if the hackers are still at large, they will be able to set a new one up again very quickly.
One issue complicating matters is whether IT security companies should allow or hamper the FBI’s trojan in their detection software. Technology consultant Graham Cluley argues that security software should not exempt the FBI’s viruses since they could be intercepted and used for ill.
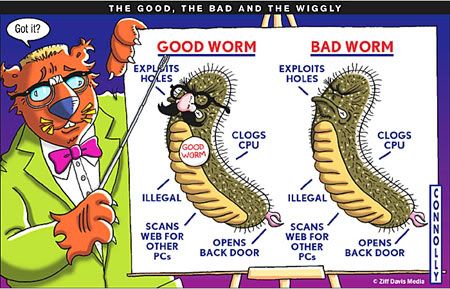
In a world of anonymising proxies it's not surprising at all to hear that the computer crime authorities might be taking a leaf out of the hackers' book to try and identify the bad guys, but here's the question I think is really interesting...What should computer security companies do about this?
I mean, the FBI would probably love it if we included a secret backdoor in our security products which meant that we turned a blind eye to their Trojan horse, and didn't detect it. After all, if an anti-virus program intercepted CIPAV and labelled it as "the FBI spyware Trojan" that would probably mess up their investigation a little.
<...>
If the FBI plant a Trojan horse like CIPAV on a PC under suspicion, they are effectively placing a weapon directly into the hands of their adversaries. The code could be easily adapted and new variants created with criminal intentions in mind. Once the Trojan was released, there would be no way of knowing who would use it to spy on whom, and with what consequences. Ironically, the FBI could even fall victim to its own code. For these and other reasons, security companies should take a very simple policy regarding spyware: detect all of it, regardless of who wrote it.


