The blog Cannonfire, which closed the case yesterday on the so-called "Weinergate" affair when it demonstrated conclusively how anyone could use a simple technique to publish any picture they wanted to another person's Twitter stream, now reports that yfrog.com has disabled the e-mail service that enables such exploits, thereby acknowledging the existence of a security problem and tacitly acknowledging that it has been abused. In short, it is no longer possible for a reasonable person to believe that Rep. Weiner was not framed by an outside party.
To make a long story much shorter than it deserves: Every Twitter user who uses yfrog to store photos for posts (I'll be cold in my grave before I ever call them "tweets") is given an e-mail address in the form [account_name].xxxxx@yfrog.com, where xxxxx is a short string of alphanumeric characters. Any time an e-mail message with an attached photo is sent to this address, the photo is automatically uploaded to yfrog.com under the recipient's account and posted to the recipient's Twitter feed as a publicly viewable message. Both the yfrog photo and the Twitter post would appear to have been posted by the e-mail recipient, and there would be no apparent connection to the e-mail sender.
The Cannonfire post explained clearly how one would do this, and blogger Joseph Cannon kindly established a Twitter account, @gdowson153, for use in demonstrating how the exploit works. Never one for believing others about something I can easily verify myself, I sent a picture I created to gdowson153.gudom@yfrog.com, the upload address for the gdowson153 account. You can see the picture at yfrog.com here, and the resulting automatic Twitter post here. I never had access to gdowson153's password or any information related to this account other than the above e-mail address. Many others were inspired to try the same technique, resulting in a humorous parade of random images posted to the gdowson153 Twitter account. (For a nice illustrated tour through this exploit, see Dreggas' valuable diary here.)
How might one obtain the secret e-mail address required to upload photos to another person's account? There are a number of possible ways. To a non-technical person, it might not be evident that this address should not be shared. If someone sent a photo to their upload address and CCed someone else in the same message, or forwarded a message from their Sent folder to another party, the address would be visible to anyone receiving the message. A potentially more likely approach, explored by Rachel Maddow's blog yesterday, would be to simply brute-force it. There are approximately 11.9 million possible combinations of five or fewer Latin letters—a lot for a human to work through, to be sure, but computers are very very good at doing repetitive tasks fairly quickly. One could easily set up a spambot to send messages to every possible e-mail address in question until finding the one that works. The whole process could be done in several hours. (Edit: The number of possible "words" that must be tried is apparently much, much smaller than 11.9 million. For details, see this post from the still-hard-to-believe-how-rehabilitated-they-look-today Little Green Footballs blog.)
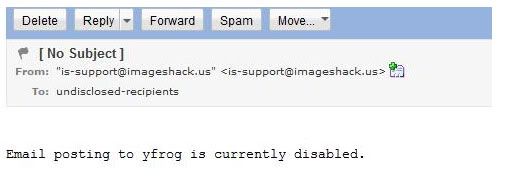
Shortly after this technique was revealed, it seems, Yfrog disabled the upload e-mail service.
Yfrog has not issued a statement about why this service has been disabled, but I think we can assume it is not a coincidence. Bear in mind that the site's operators would have access to all of their server logs and it should be a fairly trivial task to determine exactly which e-mail account had been used to send each picture uploaded to yfrog using the e-mail service, even if the site itself had not been architected to store this information with each photo as internally visible metadata. If the supposedly incriminating photo had been uploaded to Rep. Weiner's account from an e-mail address he had never used before, this would be immediately apparent.
I look forward to learning the results of the internal investigation that Yfrog is surely conducting or has already conducted. Until then, as is so often the case, we may turn to Occam's razor to help us decide which of a number of competing scenarios to believe.
We could believe that a very motivated right-wing blogger who'd already displayed an unhealthy obsession with Anthony Weiner's personal life might take advantage of a casual technique available to anyone—probably using a throwaway e-mail account and not expecting to be caught—to frame said member of Congress using a photo that, despite being suggestive and certainly harmful to his reputation, is nevertheless impossible to associate with him specifically (unlike, say, certain other photos), aided and abetted by a man who is known to be a serial liar.
Or we could believe that Dan Wolfe and Andrew Breitbart are the ones telling the truth here, and that a member of Congress whose intellect and judgment most of us have long respected experienced a brain failure so colossal in its scope and impact as to cause him to send a suggestive photograph to a college student over a public communication channel on which it would be seen by any and all of his hundreds or thousands of followers, only to completely regain his senses approximately four minutes later.
The choice, dear reader, is yours. When making it, be aware that you may be called upon to account for it in some capacity in the future.
(Edit: Rec List, y'all. Seems like the diaries of mine that make the list are always the ones that make me want to shower after writing them. Also: The mysterious @patriotusa76 makes TheSmokingGun.com. Drip... drip... drip...)


